Forget about being secure
If you can only spare 30 seconds skip to the test at the end of this blog post.
During the recent ransomware crisis it was quite understandable for people to be upset about disruption to businesses and public services. It is also understandable that leaders of these organisations rushed to announce actions to make their systems secure. This is all understandable but, in some ways, it is also naive. More cyber-attacks will come and will cause more damage than we have seen so far. We need to take a more nuanced look at the problems and some practical responses.
The illusion of complete security
In the noise and excitement of a crisis only simple messages seem to get through. For IT security and information security the diagnosis often seems to be very binary.
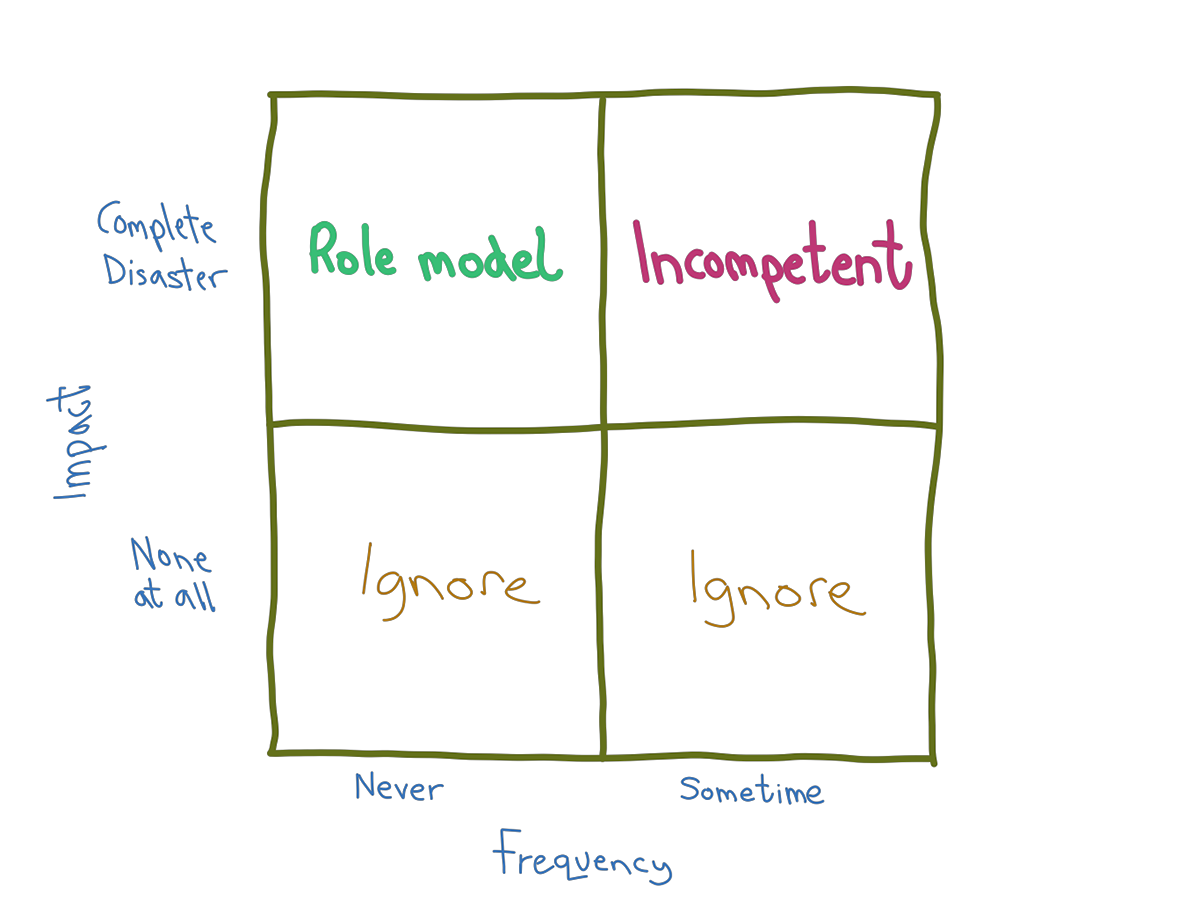
Incidents are happening all the time but most get ignored. If an organisation falls victim to a high-profile attack then we must conclude they are hopelessly incompetent. Pressure will mount to copy IT security measures from organisations which are, quite clearly, secure because they have not succumbed this time. The goal will be to make sure a breach can never happen again.
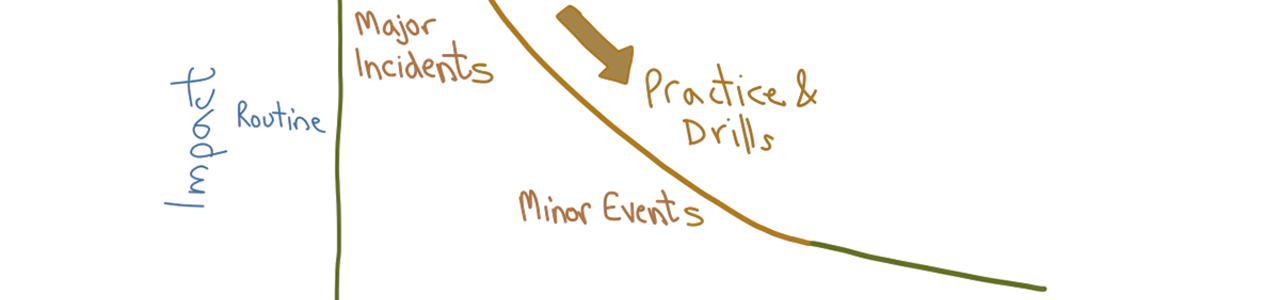
Unfortunately, there are no simple IT or information security switches that can be set to on or off, safe or unsafe. Real life is more like the chart below. Different organisations may shift the scales to reduce the frequency or impact of security problems but there is no way to shift the graph to be completely safe and secure. All of our IT (which will soon include cars, TVs, fridges and utility meters) is under a constant, withering attack. Much of this is generated by tireless banks of computers outside your organisation but, to do any real damage, it often requires accidental or deliberate human cooperation. We can set up barriers to defend our organisations but, eventually, something will go wrong. It is likely that the source of your next security breach is already working in your organisation and is getting glowing reviews for their performance. It might even be you.
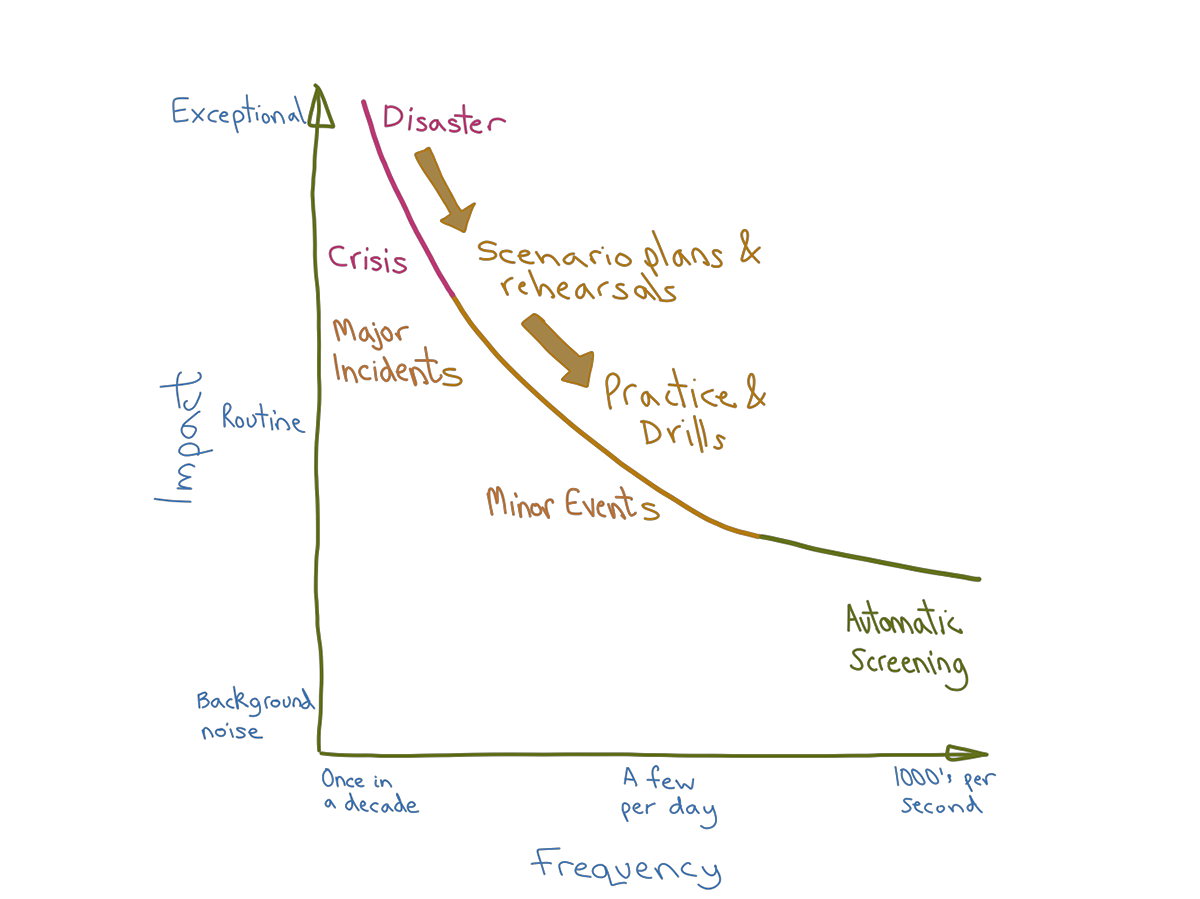
This has strong parallels with other kinds of security and safety which are all characterised by uncertain trade-offs between various degrees of risk and imperfect mitigations. For example, years of improvements to road safety have not completely eliminated accidents. As driving becomes more digital it is as good as certain that an autonomous car will kill someone because of a software bug or a deliberate hack. That is not a good reason to block the technology because, on balance, autonomous cars may make our roads even safer. Similarly, there are a lot of things we can do to make IT more secure (much of it is quite easy and cheap) but our systems will never be completely secure and risk free.
Insecure but prepared
If it is impossible to have completely safe and secure IT then what approach should CIOs take? Should you reach for specialist tools and techniques, model threats and vulnerabilities in detail and deploy machine learning systems to spot sophisticated attacks? Perhaps, but this is not a good place to start. High-end security tools and techniques can be expensive, hard to use and will provide little additional security if you have not already got the basics right. Other forms of safety and security have had much more time to mature than IT and are a good source of reference. Here are some of the basic elements which should appear in your IT security portfolio.
- Remain alert and keep learning from others - There is a good chance that you won’t be the first victim of any new threats which emerge so collaborate with your peers through the various regional and industry networks to keep one step ahead.
- Provide information and training - Keep your users up to date on what they need to do to stay secure while getting their work done. Help your staff keep their personal IT safe and don’t forget your customers and suppliers as any of these could become a route for an attack.
- Use decent quality materials and good maintenance - Take care when selecting equipment, software, IT services and people to join your team. Make use of the plentiful advice available to configure your IT in a secure way and keep it in good condition with regular reviews and updates.
- Install smoke detectors and alarms - Set up and tune tools and processes to monitor IT activity and trigger action if necessary. Trigger your IT security alarms regularly to make sure they work properly.
- Consider fire blankets, extinguishers, first aid kits - Have equipment, tools and procedures ready to use to respond to common problems. Basic asset management and backups are an absolute minimum. Test these regularly so you can be confident they will work when you need them.
- Call emergency services when appropriate - It will not be economical to cover every potential situation internally so make use of specialist services where necessary (e.g. penetration testing) and set up appropriate stand-by and call-off arrangements.
- Run fire drills - Keep all of your arrangements under review. Set up regular exercises to simulate major problems and give your people and partners a chance to practice. Don’t wait for a real attack to find the flaws in your emergency plans.
Have you done enough to make your organisation secure?
As you work through these items you will keep finding more opportunities to improve your security but there will also be other claims on your limited time and resources. How much security is enough? Try this little experiment:
- Imagine, in spite of all the measures you have taken, an attacker breaks into your IT and disrupts your operations or exposes some highly sensitive information
- Are you clear on your next steps including what you are going to say in any public announcements?
- Can you explain what IT security measures you had in place?
- Do the trade-offs you made still seem reasonable?
Is it hard to answer these questions or do the answers make you feel uncomfortable? If so, you and your executive peers have more work to do.